Overview#
I have used Docker and containers for multiple projects and CTFs in the past year. Although I had such a horrible time in my first attempts especially when building the SOC Home Lab when I managed The Hive, MISP and Cortex. So basically if ChatGPT can do it, then the installations and configuration succeeds. Otherwise, I give up since I saw it as very complicated due to the hype out there on the fancy Devops, DevSecOps and that kind of crap.
Fast forward, hosting 2 national CTFs and 2 internal CTFs and getting my hands dirty with running up, down, attaching and managing containers got a bit better and I got the idea more.
So here I am, trying to learn Docker the right way to really know what is happening within and what is the containerisation philosophy.
I will discuss Linux Containers. Of course containers aren’t only implemented with Linux, that can be done using Windows and Mac too.
Linux Namespaces#
Docker Architecture#
What caused me, and probably you, big trouble, is how should I look at these Docker containers. What should I even call them? Docker? Containers? Not that I haven’t looked it up, but it was so vague.
Also are they Virtual Machines? What the fuck are they exactly? If they were VMs then where is the hypervisor?
Containers as Linux Processes#
To kick things off, here are similarities between Docker containers and Linux processes to help us visualize what containers are:
They are real Linux processes: every container is backed by 1 or more Linux processes. We can visualize this by
ps aux.Directory in the same Kernel: No other kernel for the containers and no hypervisors needed.
Signals work normally:
docker kill -SIGTERM <container>maps directly tokill -SIGTERM <PID>.
Containers as NOT Linux Processes#
This is where things get interesting.
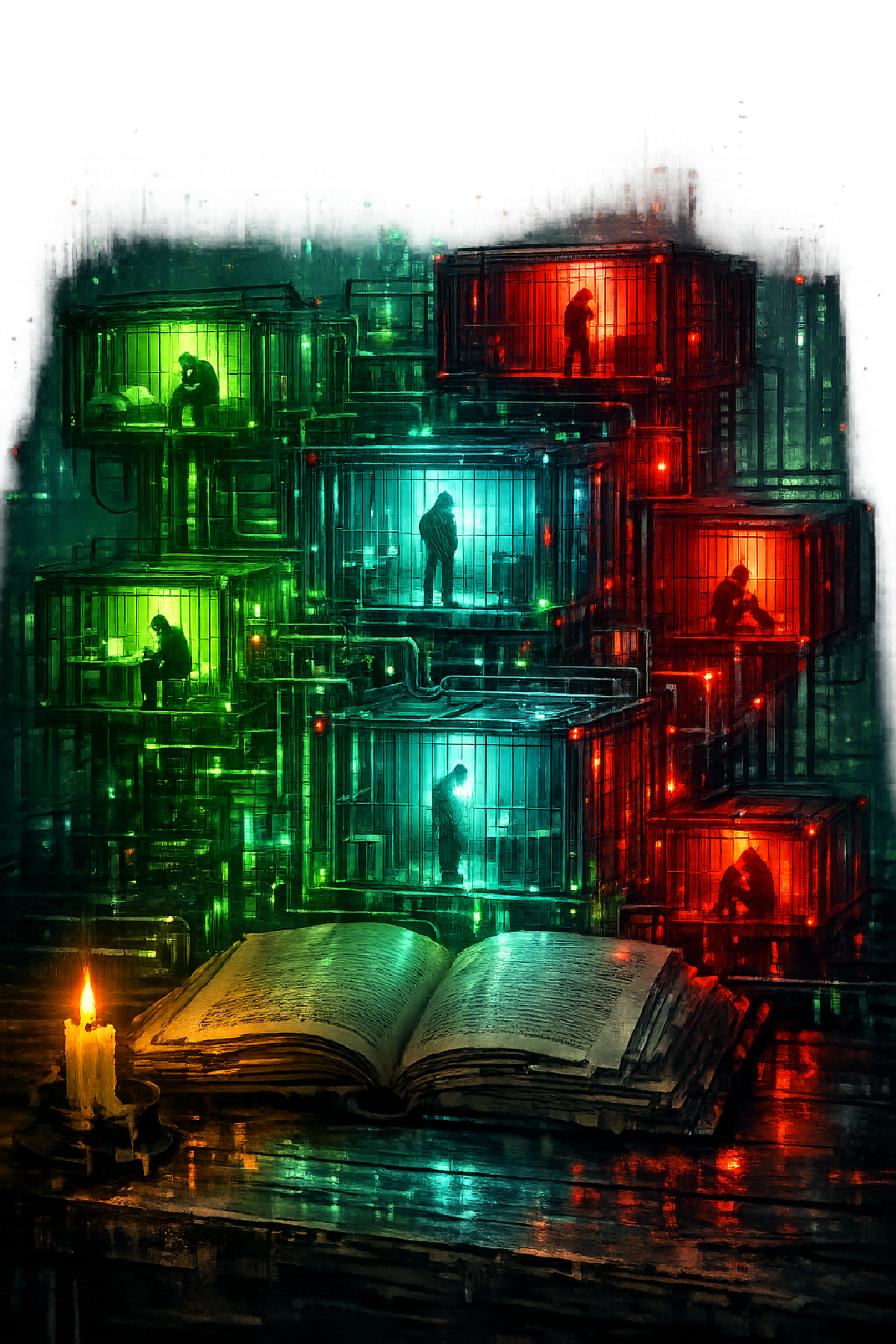
Containers use isolated environment on top of the Linux Kernel of the Host machine. That is done using Linux namespaces. As specified above, namespaces is a feature that makes a process see its onw processes, filesystem, network interfaces and all. Thus, they share the same Kernel, yet each set of processes is seperated (Thus the name of this blog post.)
Furthermore, containers are limited by cgroups, a Linux feature that limits and sets the boundaries of the CPU and memory usage, I/O resources that containers can consume.
So Linux Containers aren’t literally Linux processes, but they’re more like an isolated environment of a suite of processes with managed resources that are configured and isolated.
Open Container Initiative#
It is very wrong if I say there not much to say in this matter, but here’s a resume on what is the OCI.
Simply put, OCI is an initiative to standarize the container architectures across the maintainers and other container projects worldwide. OCI defines how and what we can do with a container, how it is defined and how it works internally.