About
Table of Contents
Introduction#
Taha Marouani, a persistent, serious and ambitious Telecommunications Engineering student.
A self-learner who’s dedicating his time to focus on what really matters: Touching grass, making a change, and developing a solid career.
Armed with passion for Cybersecurity, Philosophy and Books, I’m finding my purpose through this non-sense by learning.
Academic Journey#
Engineering Degree in Telecommunications
2024-2027
With a strong focus on Signal Processing, Telecommunications, and Physics, I study the engineering principles behind how information is transmitted, processed, and received, contributing to the advancement of modern communication infrastructures.Operating SystemsLinuxCisco Packet TracerHuawei eNSPBashNetworkingCC++C#.NETNode.jsNext.jsReactNational Entrance Exams for Engineering School
2024-2027
As a PTSI student within the CPGE program, I underwent an intensive and rigorous scientific training focused on mathematics, physics, and engineering sciences. This was a very rewarding journey as it enhanced my analytical thinking, problem-solving abilities, and capacity to work under pressure (lots of pressure), all while building a solid foundation for advanced studies in engineering having the most important skills as an engineer.PhysicsMathsChemistryMachanicsElectronicsPythonProblem SolvingCritical ThinkingEngineeringWork under pressureBaccalaureat Degree
2020
Technical Experience#
Cybersecurity Internship - Biat IT
Summer 2025
- Created an on-premise Open Source SOC Lab: Wazuh, TheHive, MISP, Cortex.
- Automated the deployment of different components using Docker containers.
- Reviewed and enhanced Threat Intelligence reports of previously filtered incidents.
- Studied and analyzed XDR/NDR logs to trace lateral movement attempts.
- Analyzed recent severe alerts and enhanced the final provided report.
- Performed a Threat Hunt based on traces from a critical recent incident.
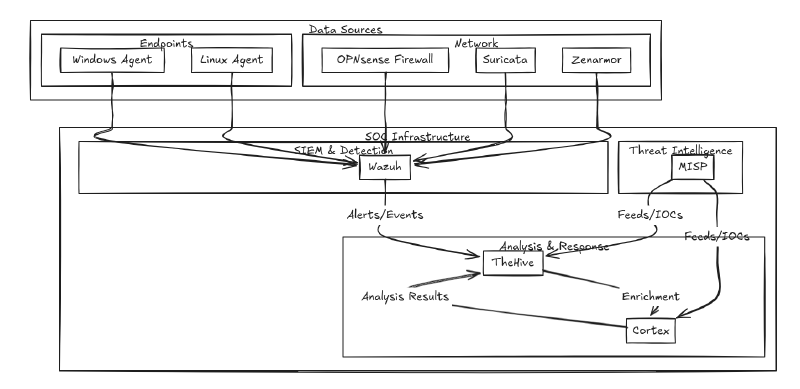
The Open Source on-premise, SOC Architecture I built. SOCFirewallWazuhIDSIPSThe HiveMISPCortexSIEMSOARActive DirectoryWindowsThreat HuntingThreat IntelligenceSecurity OperationsLog AnalysisMalware Analysis Project
November - April 2025
- Created an on-premise and cloud Malware Analysis Lab.
- Analyzed Zeus Trojan - Banking Version and WannaCry Ransomware.
- Performed Static and Dynamic analysis on different samples.
- Reverse Engineered multiple samples and classified differences in tradecraft.
- Replicated malware behavior and re-created their base source codes.
- Researched coverd evasion techniques and tactics and mapped them to MITRE IDs.
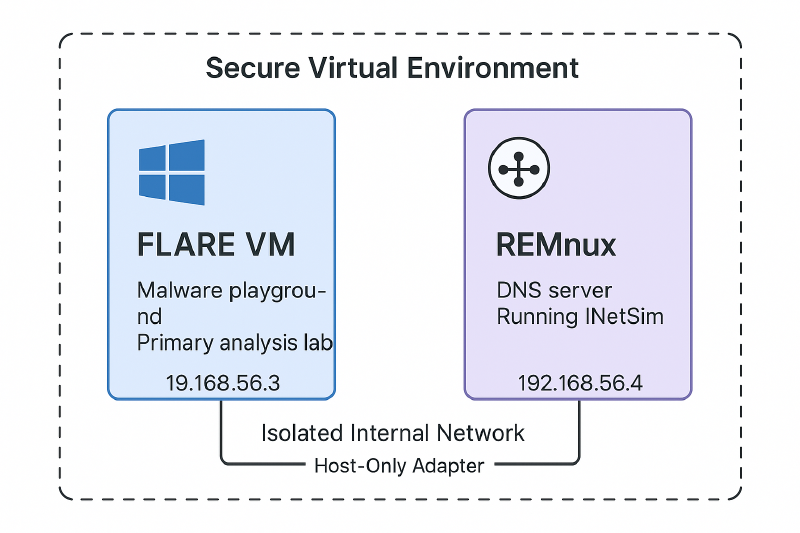
Malware Analysis Lab Architecture. Malware AnalysisReverse EngineeringBinary AnalysisStatic AnalysisDynamic AnalysisAssembly (x86)Windows PEAnti-Debugging & EvasionC2 CommunicationWiresharkProcMonIDA / GhidraMITRE ATT&CK MappingTrojanRansomwareShortcodes
AWESOME
With other shortcodes






Another Awesome Header
CTFs and Ranking#
HackTheBox Profile#
Since Summer 2025, I started seriously and methodologically attacking HackTheBox Labs and sherlocks.
You can find my profile stats down below.
CTFTime Profile#
I’m a part of Curiosity, a Tunisian CTF Team formed by July 2025.
Currently, we’re ranked Tunisia’s Top 1 and 262nd Globally.
I currently focus on:
- DFIR
- Reverse Engineering
- and some Binary Exploitation tasks.
You can view my CTFTime Profile Here .
There are no articles to list here yet.